North Korea’s new cybercriminals

For decades, North Korea sent workers abroad to build buildings, cut timber and slave in factories. Their wages in dollars flowed back to Pyongyang.
Then came sanctions over the regime’s rogue nuclear development program. They made that foreign currency-earning system far more difficult.
But the regime did not give up. Instead, it appears to have redirected its attention to somewhere far less visible, from construction sites to computer networks.
These operatives do not put on hard hats or travel to remote forests. They work behind computer screens, infiltrating companies and digital platforms across the world, crossing borders via keyboard. Visas and residence permits are not necessary. In fact, they do not even need to be physically present in the host country.
As a result, they are largely beyond the reach of conventional labor regulations and sanctions regimes.
The revenues they generate are now believed to rival, or in some cases exceed, the income once produced by overseas labor programs.
According to the U.S. Treasury Department, in a report submitted to Congress in March, North Korean cybercriminal organizations have generated vast revenues through the theft of digital assets.
“DPRK cybercriminals have generated billions of dollars of revenue in digital assets through theft,” it noted. The regime relies on schemes involving digital assets to fund its weapons of mass destruction and ballistic missile programs, it said.
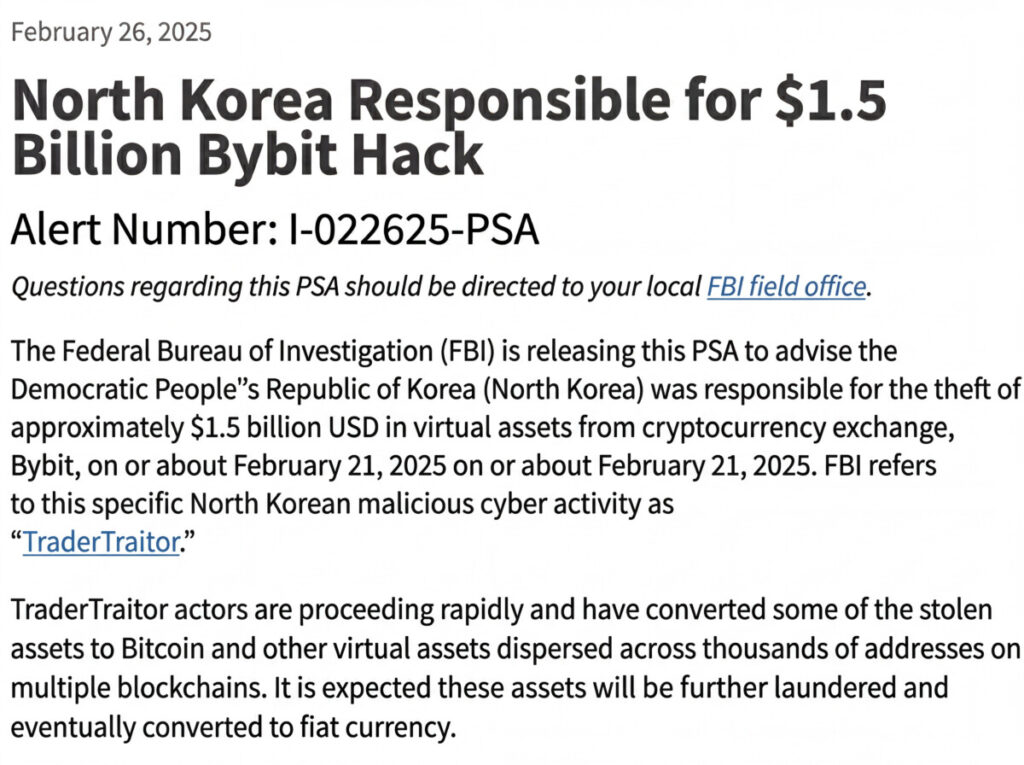
The scale of these operations has grown rapidly. The report described a February 2025 attack in which North Korean cyber actors stole $1.5 billion in digital assets from a digital asset service provider in the largest cryptocurrency heist ever recorded.
From January 2024 to September 2025 alone, North Korea is estimated to have stolen at least $2.8 billion in digital assets.

Investigators say North Korean actors have become particularly adept at exploiting the architecture of the cryptocurrency ecosystem to launder illicit funds.
One commonly used technique is “mixing,” a process that pools and redistributes cryptocurrency transactions to make them difficult to trace. Criminal groups frequently combine mixing with other blockchain tools such as “bridging” — transferring assets across different blockchains — and “swapping,” which converts one digital token into another.
These methods complicate the work of law enforcement and compliance systems.
“Criminals commonly use tools like mixing, bridging and swapping to introduce challenges for investigators attempting to trace illicit digital assets,” the Treasury report stated.
North Korean operators often layer these techniques together. Stolen tokens may first be exchanged through decentralized exchanges, then routed through mixers before being consolidated into self-hosted digital wallets. From there, the funds can move through multiple blockchain bridges or token swaps before eventually being converted into cash.
The process is designed to move money quickly and fragment the transaction trail.
“DPRK actors rapidly move funds through mixers and other obfuscation techniques,” the report noted.
Another frequently used tactic involves converting stolen cryptocurrency into stablecoins. These are digital assets pegged to traditional currencies. Illicit actors may route stolen Bitcoin or other tokens through mixing services before rapidly swapping them into stablecoins, which can then be transferred to new wallets and separated from the original criminal transactions.
This technique can help circumvent anti–money laundering (AML), counter–terrorist financing (CFT) controls and sanctions monitoring systems.
According to the Treasury, more than $37.4 billion in withdrawals from over 50 blockchain bridges since May 2020 have been denominated in the two largest stablecoins by market capitalization.
During the same period, those bridges received approximately $1.6 billion in deposits originating from mixing services. Some $900 million of them flowed through a single bridge that faced criticism for failing to intervene while actors linked to North Korea laundered proceeds from a digital asset theft.
Decentralized finance, or DeFi, has also become part of this ecosystem. DeFi platforms allow users to exchange or transfer digital assets without centralized intermediaries, making them attractive tools for actors seeking to obscure financial trails. North Korean cyber operators have been observed using decentralized exchanges, blockchain bridges and mixers to conceal the origin of stolen funds and evade regulatory scrutiny.
Yet the same transparency that makes blockchain transactions possible also leaves traces.
Because most public blockchains record transaction histories permanently, analysts in both the public and private sectors are sometimes able to reconstruct the movement of illicit funds through the DeFi ecosystem.
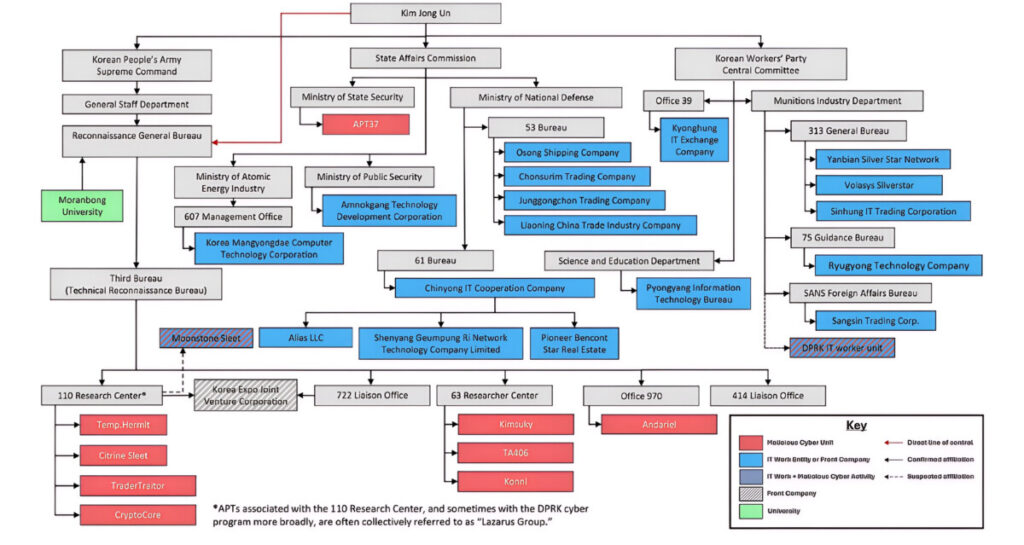
North Korea’s cyber capabilities have drawn increasing concern from the U.S. intelligence community.
In its March 2026 Annual Threat Assessment, the Office of the Director of National Intelligence described North Korea’s cyber program as both “sophisticated and agile,” particularly when combined with the regime’s strategy of placing IT workers in foreign companies using falsified identities.
These operatives may gain employment with unsuspecting firms, allowing them to collect intelligence, facilitate cyber operations or bypass corporate security systems from within.
According to the assessment, North Korea’s cyber activities focus on evading financial sanctions, stealing funds to support its military programs, and conducting cyber espionage to fill technological gaps in weapons development.
Cryptocurrency theft and other financial crimes alone are estimated to generate at least $1 billion annually to fund the regime’s weapons programs.
Viewed in historical context, the shift from physical labor to digital infiltration represents an evolution rather than a departure in North Korea’s foreign currency strategy.
The crucial difference is that the new pipeline has no borders.
The country’s shadow economy has not disappeared. It has simply changed form. It may already be further along that transition than many policymakers realize.
- May Day and the unheard cry beneath the propaganda - May 13, 2026
- North Korea’s new cybercriminals - April 15, 2026
- North Korea and its money-making overseas workers - April 9, 2026

ci4bfg